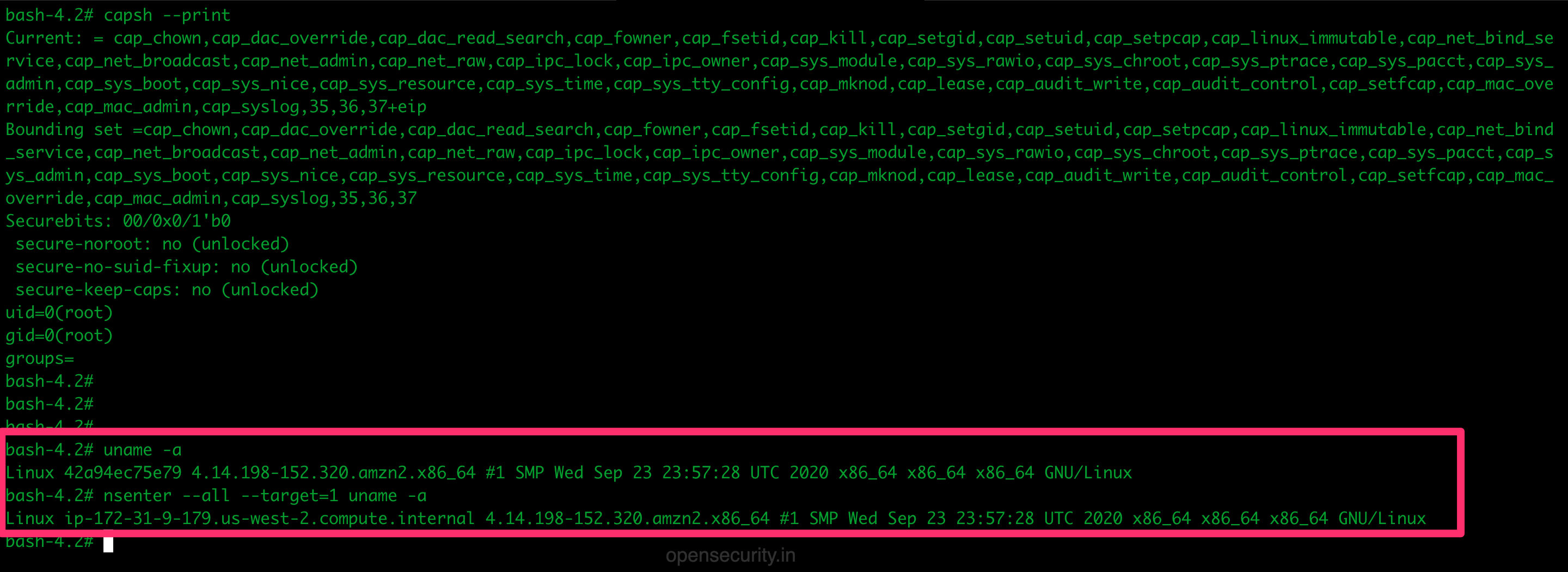
OpenSecurity on Twitter: "Friday Pentest Tip: Got access to a privileged container/k8s cluster? Escape to host with nsenter. nsenter --all --target=1 uname -a More tools and techniques: https://t.co/6az4ENi421 https://t.co/XL3f3L9IpQ" / Twitter
Why am I able to bind a privileged port in my container without the NET_BIND_SERVICE capability? | by Olivier Gaumond | Medium
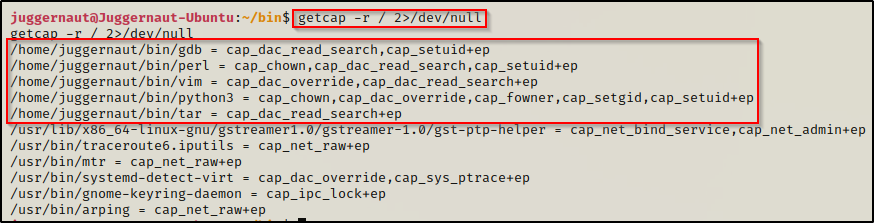
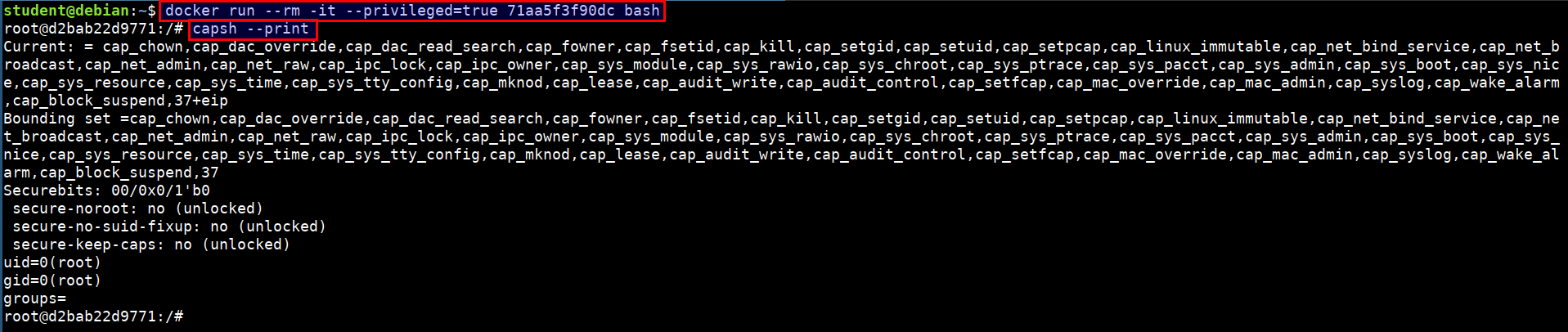
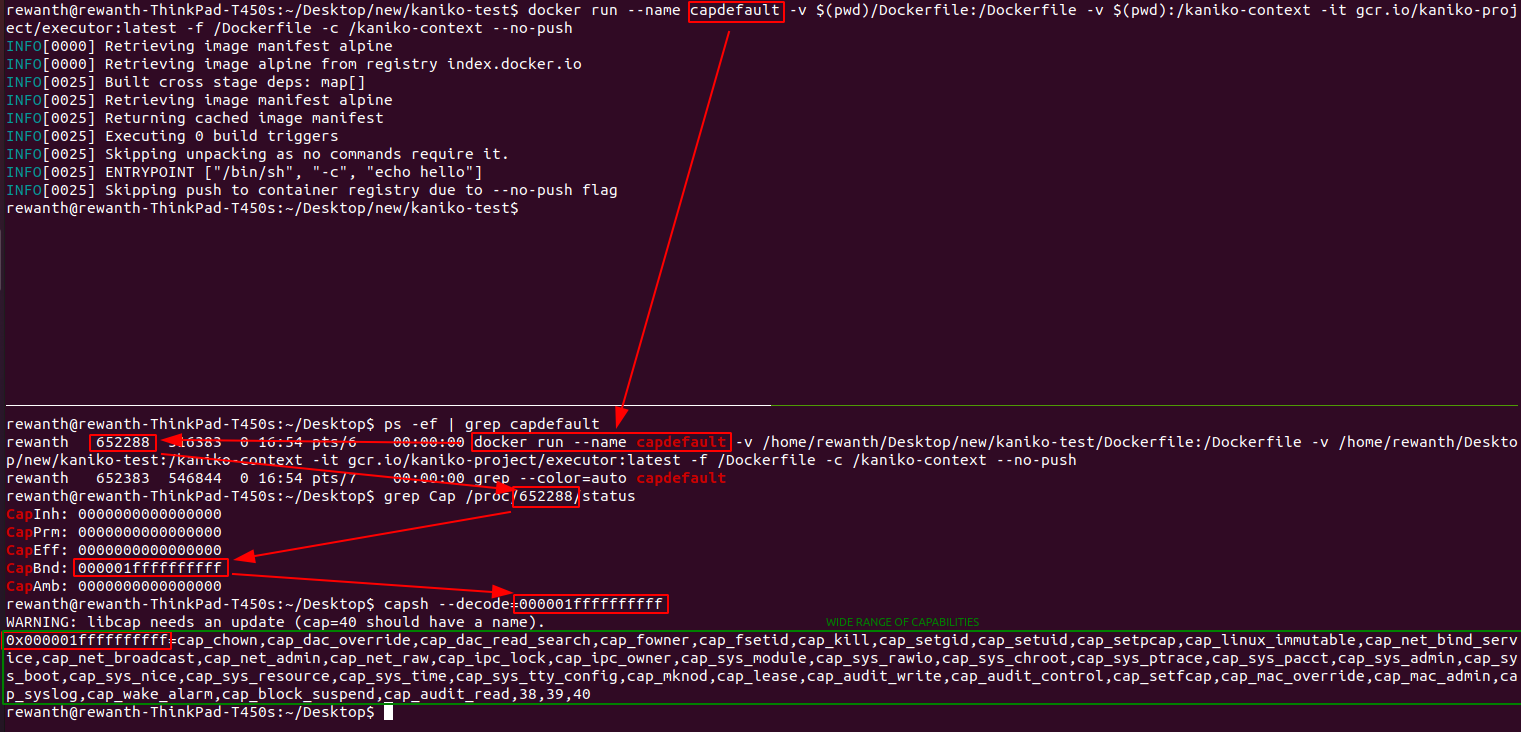
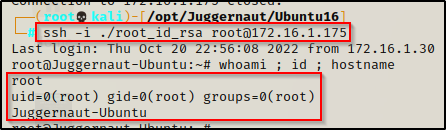
![[Linux Security] Understanding Linux Capabilities Series (Part I) | by Nishant Sharma | Pentester Academy Blog [Linux Security] Understanding Linux Capabilities Series (Part I) | by Nishant Sharma | Pentester Academy Blog](https://cdn-images-1.medium.com/fit/t/1600/480/0*3gGqpTBqD2flWxWh)